What's quantum cryptography?
A quantum introduction
Quantum physic is getting discovered during the 20th century and is made of multiple theories that seem to solve current classical physic problems. Actually, it is so important that where quantum laws applies, Newton’s don’t. And vice versa. It describes two worlds where physics laws are just not the same. And this is why it radically changes the cryptography concept. We do not use commons physics laws but we use quantum one’s. And as we will see, these new rules allow us to be faster and stronger.
How does quantum works
Quantum laws are describing the behavior of particles and atoms. To understand how it works and why it is so great, we need to explain some concepts:
- Quantum superposition
This principle explain that any two or more quantum states can be added together to form another valid state. This new state is commonly described as the sum of the compound states. We can visualize it as vectors in geometry. Any vector can always be designed as the sum of two or more vectors.
In quantum computer we use qbits, which are the quantum equivalent of bit. They are a superposition of both the “0” state and the “1” state. Keep in mind that you can’t know what the state of the qbit is until you measure it. This measure will fix a value which can give either 0 or 1, nothing else. Multiple measures will not always give you the same result even though it’s made on qbit with the same quantum state(which we are not able to reproduce currently). Once you’ve made a measurement on a specific qbit, this qbit state is fixed forever into a 0 or 1. This is caused by the interference of the measure.
To make a real experiment we commonly use polarized photons. Photons are particles but they’re also waves, and it gives them properties that we can use in quantum mechanics such as angles. The polarization of a photon is the angle taken by its wave. This angle can be stopped with a filter:
We can then use these photons through optic fiber as qbits.
- Quantum information theory
It regroups 4 theorems which are:- no-teleportation theorem, which states that a qbit cannot be (wholly) converted into classical bits.
- no-cloning theorem, which prevents an arbitrary qbit from being copied.
- no-deleting theorem, which prevents an arbitrary qbit from being deleted.
- no-broadcast theorem, Although a single qbit can be transported from place to place, it cannot be delivered to multiple recipients.
We’re particularly interested in two of them: the no-cloning and the no-deleting, as they are both used to ensure the communication safety. We’ll see that both of them will assure the communication safety.
Using quantum in cryptography
Now let’s see how Bob and Alice can generate and exchange a key for their further communication noticing when Eve tries to steal some information along the process.
First, Alice and Bob need two communications canals. A first one, quantum valid, like optic fiber to transmit photons, and a second one, more classical, like emails or phone. We assume that this usual canal is as safe as possible, which means protected by currents non quantum algorithm.
The quantum canal is known to be safe against active intruders by the laws of quantum physics (an active intruder can modify or destroy the information he retrieves, the passive one can only listen to it). Indeed, thanks to the no-cloning theorem, Eve cannot intercept a photon and re-emmit one without implying a change that would have high chances to be discovered and the no-deleting theorem implies that she cannot delete any information.
So here’s the process Alice and Bob follows:
Step 1: Alice chose to assign a polarization base for the bit 0, let’s say horizontal and 45° photons, then for the bit 1, vertical and 135° photons.
Step 2: Alice generates a random string of bits and send the polarized photon equivalent she just decided at step 1.
Step 3: Bob receives every photon and randomly choose for each one a polarization base to measure them. He then interprets the measurement as a 0 or a 1.
Step 4: Out of the quantum communication way, Bob then tells Alice each polarization base he chose for every photon.
Step 5: Alice answers and for every good choice, which Bob had 50% to get, they then share the same value.
Step 6: Some of this shared information will be sacrificed to check if anyone was listening along the process by comparing them between Bob and Alice. Indeed, if too many information was not received or if too many sacrificed bits are not the same, they might think someone listened. This step purpose is to maximize the enthropy, it add a random selection factor:
{< image src="/images/post/step6_explanation.PNG" caption="" alt=“vipère péliade” height="" width="" position=“center” command=“fill” option=“q100” class=“img-fluid” title=“vipère péliade” webp=“false” >}
- Step 7: Keeping only the shared information not sacrificed, Bob and Alice now have a perfectly random and secret key to protect their future communication. They can add extra steps of mixing the information left to maximize it’s randomness.
Here is the scheme showing us these steps:
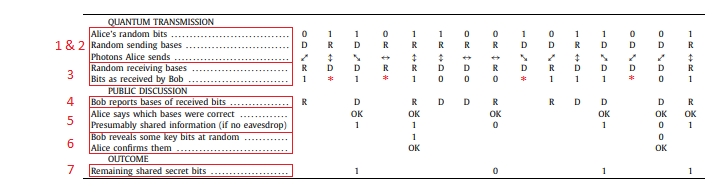
Quantum cryptography: Public key distribution and coin tossing Charles H. Bennett, Gilles Brassard
Red dots reflect the fact that in reality, some photons might get lost or not be correctly handled by the detectors.
The R and D letters stands for Rectilinear and Diagonal, it refers to the randomly selected polarization base.
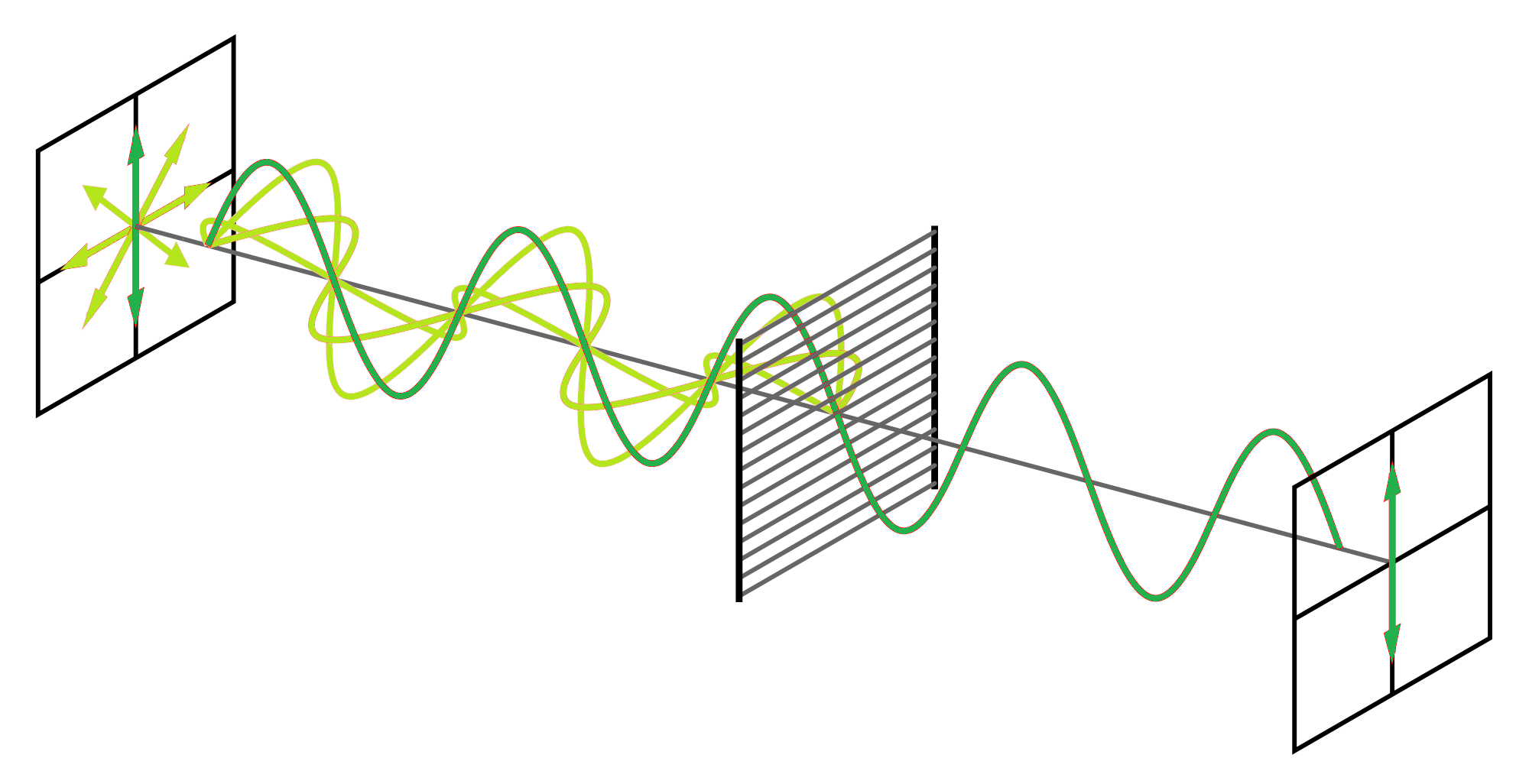
These two base describe the angle taken by the wave of the photon as it act like a particle and like a wave:
This protocol seems to be described first in december 1984 in the scientific journal Theoretical Computer Science
Things to keep in mind
Quantum physic is not itself a true revolution. The discovery of the laws that underlay it has been used in numerous technical evolutions for many years such as transistors or in medicine.
Latest discoveries as well as popularization made by press have recently unveiled the subject to the public the way they love to do it, with much drama and without explanation, leading to misunderstanding and false ideas.
The multiple technologies in quantum computing and particularly the quantum distribution have opened many usage options such as transfer security in industry, between government, in the army, or security of the datas in banks, social networks… Quantum physic, more generally can also be used in financial prevision or meteorological prevision.
We also have to keep in mind that, quantum cryptology is a well-known threat to some algorithm like RSA or Diffie-Hellman that are based on particular mathematical methods but cannot be effective against other algorithm like NTRU for example. Global systems security is not as much threatened as media says.
Finally, even if the principles of quantum physics have been discovered near 1900, the mastering of it, so to speak, and it’s usage in cryptology is extremely new, and we will have to wait again some years before a day to day usage of them. Indeed, the IT science in cryptology depends directly of what is discovered in other domain like in quantum physic directly or in the mastering of the stabilisation process of the qbit. All of this is for now extremely costy and needs a lot of energy to be stable.
To go further
If you’re still reading down here, thank you. I’d be really happy to receive any comment or to answer any question (or try at least) on the subject via my email on the author section (Thanks to put the “quantum” word in the mail subject for sorting purpose)l For some of you that would go further on the subject, here are some thesis or documents that might interest you (they are all free and available on the net):
- Quantum cryptography: Public key distribution and coin tossing Charles H. Bennett, Gilles Brassard
- Quantum Computing: Progress and Prospects (2019)
- NIST Post-Quantum Cryptography Standardization
- Dispositif de distribution quantique de clé avec des états cohérents à longueur d’onde télécom
- Introduction a la cryptographie quantique et au calcul quantique Pierre Rouchon (2017)