Feedback on OWASP AppSec Europe 2017
This year, I had the great opportunity to attent the OWASP AppSec Europe 2017 , in Belfast, Thursday 11th & Friday 12th May.

I learned a lot about Angular and JS frameworks vulnerabilities & protections (that was my first wish). It was very helpful and I tried to add the most insights from this great event into my talk about Angular security hardening during the TechForum 2017, our annual internal IT event, at Worldline France.
- The AppSec Europe Conference
- What happens in a AppSec Europe conference?
- Feelings
- Followed talks
- Conclusion
The AppSec Europe Conference
This is Annual AppSec EU Security Conference, the premier application security conference for European developers and security experts.
During the pre-conference (Monday 8th - Wednesday 10th May 2017) there is the opportunity to attend one of the many trainings courses on offer from industry experts.
The main conference (Thursday 11th & Friday 12th May) offers four full tracks of talks, for pentesters and ethical hackers, developers and security engineers, DevOps practices and GRC/risk level talks for managers and CISOs
What Happens at an AppSec Europe Conference?
This is a very rich event in terms of diversity and activities
- Technical talks by security, devops and cloud experts
- Panels to discuss topics
- Training sessions for hands on learning in top security areas
- Keynotes from industry leaders
- Vendor booths to promote the latest advances in security technology
- A variety of other activities such as recruiting fair, capture the flag, security tool training, and more
Context
- 4 main tracks: “DevSecOps”, “Hacking”, “CISO” and “Development”
- 73 conferences with speakers from over 30 different contries
- 700 attendees
- 3 training days, 2 conference days
Keynotes
- Shannon Lietz. The Gift of Feedback - Movie
- Brian Honan. Looking back to look ahead - Movie
- Jeremiah Grossman. What the Kidnapping & Ransom Economy Teaches Us About Ransomware - Movie
- Jaya Baloo. Everything is Quantum! - Movie
Feelings
This event was well organized and its seems to be in a constant growing (4th time in Europe). Check out the previous conferences to get even more information on what to expect:
I enjoyed the place and talks as you can see below in detail.
Place
Belfast is a small city with lot of charms - As expected, I’ve seen lots of beautiful and historical churches and… traditional Irish pubs :) This city mixes historical and modern architectures and attract more and more IT events. Some of us had the opportunity to have a dinner at the Titanic museum , one of the best places in Belfast.
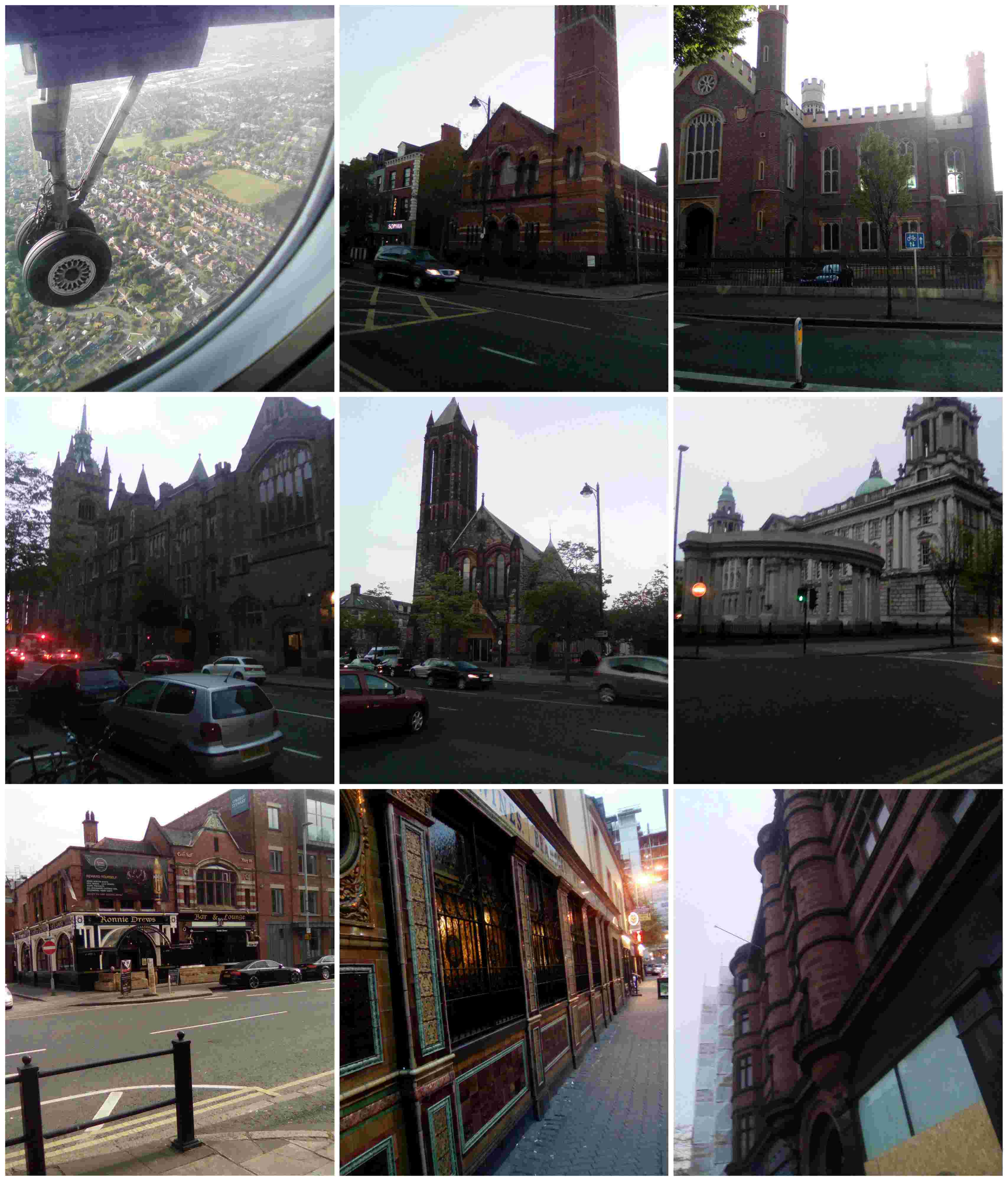
… But Belfast is not so easy to access - No direct fly from Paris - I took a tiny plane for the connecting flight between Manchester and Belfast. Within such transport, security feeling is curiously low! We’ve done several round trips before landing because of the wind. This was the opportunity to see the city from the sky!
Talks
I only followed the conferences (not the trainings, nor other activities - capture the flag, …) and I was more interested on topics related to developement/hacking for Angular applications because it’s my field of work. But I also tried to follow other talks in order to “feel the atmosphere” and identify trends.
The main tracks were the following:
- Hacking: white hat, demonstrations, capture the flag, challenges, …
- Developer: best practices to secure application, pentests, trainings, …
- SDLC (software development life cycle) : CI, tooling, methods
- DevSecOps: new trend, integrating security in DevOps
I enjoyed the hight level of the topics, fresh research results and the speakers’ skills (famous hackers/researchers and speakers : cure53 white hackers, google security team, …)
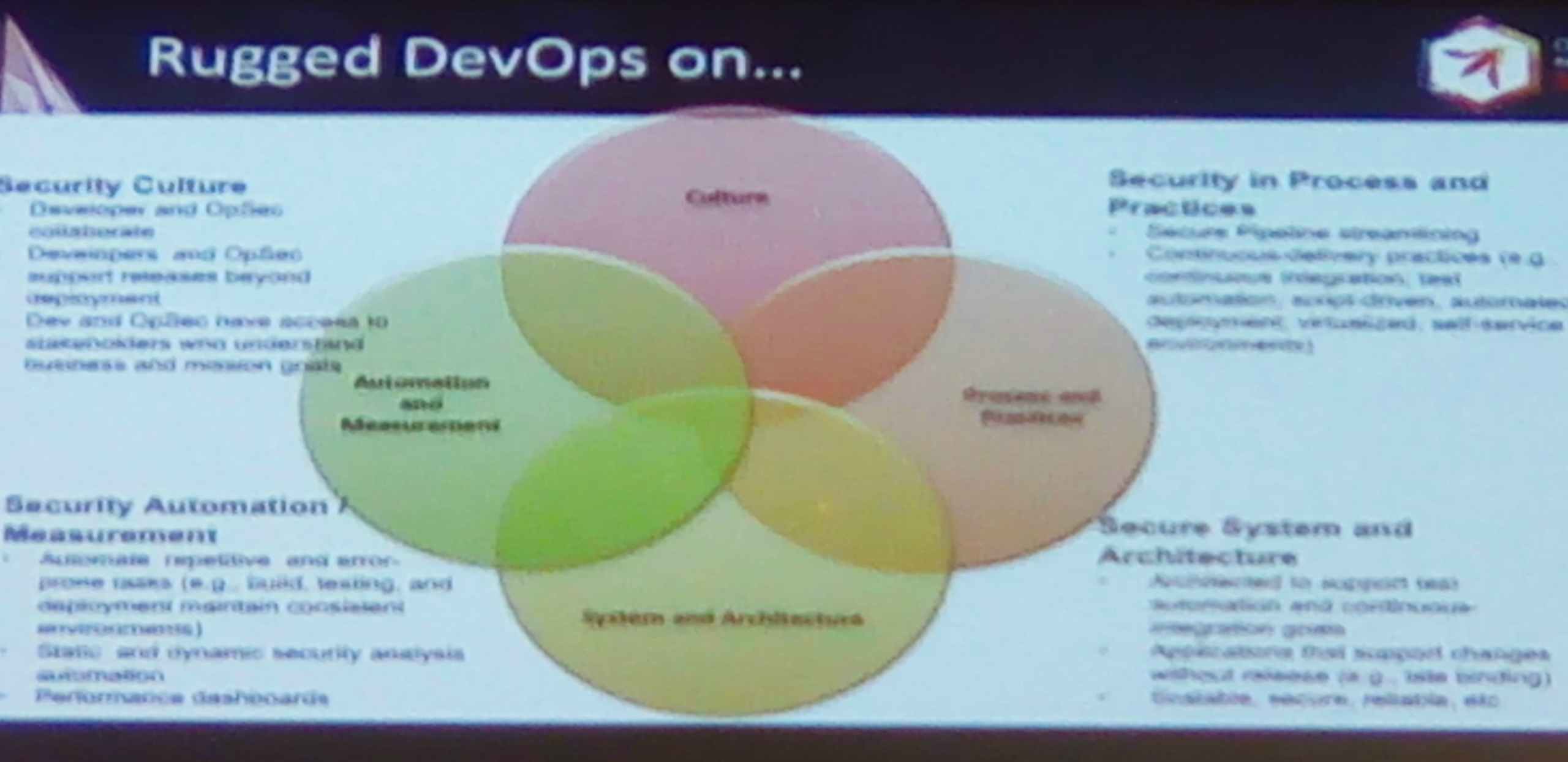
I’ve noted the huge importance given to the DevOps track which addressed the problematic of integrated security in the DevOps process (18 talks dedicated to DevSecOps!). The idea : security must fully blended in DevOps, not separated (at the begining or at the end but with), hence the word DevSecOps. Security during each of the following steps: architecture, development, CI, DI, … with dedicated tools and methods
Vendors
I also enjoyed the good opportunity for networking and discovering tools & partners (Sonatype, Hewlett Packard, CME Group, Synopsys, …).
I was interested on Web application security scanners for Single Page Applications (SPA) and how to secure Docker containers in DevOps environment (See Netsparker and TwistLock ).
I’ve also noticed an interesting product which claims protecting SPA against XSS by pre-compiling/minimizing/encryting the source code (Jscrambler ). For all these products, I got contact for futher evaluations, tests and trial installation.
Followed talks
I’ve assisted to the following talks. My priority was those related to Angular security hardening and JS frameworks vulnerabilities, mitigations and protections:
Keynotes
"The Gift of Feedback" by Shannon Lietz
{ https://blog.worldline.tech//images/post/owasp-appsec-europe-2017-feedback/owasp-appsec-europe-2017-feedback/devsecops_feedback.jpg does not exist }{: .align-right width=“300px”}
Feedback is crucial in our domain but underestimate. It makes our products better and better. Developers should implement processes to collect feedbacks in order to improve their applications. They should educate team members, users and clients to provide feedbacks. But feedback’s providers should care about the quality of their approach. Always provide positive feedbacks. Positive does not mean good but constructive. The ones that make the developer progress and allow improving their applications. Criticism and affects will just create a bad atmosphere between parties.
"What the Kidnapping & Ransom Economy Teaches Us About Ransomware" By Jeremiah Grossman
{ https://blog.worldline.tech//images/post/owasp-appsec-europe-2017-feedback/owasp-appsec-europe-2017-feedback/jeremiah_whitehat_security_randsomeware.jpg does not exist }
I was suprised by the comparison between randsomeware and piracy (from the sea). They use the same tools, process, finality and approach. I learned also about the growing of new insurance companies specialized on randsomware. They provide to their client help, consultancy, mediation, negotiation with the hackers, … They coach clients to make them behave in a certain way (don’t panic, don’t pay too soon, negociate, ask proof, provide backup, …)
Did you know that Britney Spears’ music was used to keep Somali pirates away?? Apparently thanks to/because of cultural dimissilarity… Seems to be efficient. But unfortunately, there may be too much side effects? :)
{ https://blog.worldline.tech//images/post/owasp-appsec-europe-2017-feedback/owasp-appsec-europe-2017-feedback/britney_spears.jpg does not exist }{: .align-center width=“400px”}
Other interesting facts about randsomewares in pictures:
{ https://blog.worldline.tech//images/post/owasp-appsec-europe-2017-feedback/owasp-appsec-europe-2017-feedback/randsomware_quotes.jpg does not exist }{: .align-center}
Developer
"So we broke all CSPs… You won’t guess what happened next! “, by Michele Spagnuolo and Lukas Weichselbaum - Movie
Great talk from google security team members. They provided a concrete method to migrate existing applications to Content Security Policy (CSP) - an unavoidable browser feature against XSS. They displayed how CSP 1 is unsecure (95% of CSP 1 setting are unsecure!) and how CSP 2 and CSP 3 have been improved to be efficient and flexible. They’ve shared their own experience of migrating google services into CSP (use of strict-dynamic syntax, csp-evaluator online tool).
{ https://blog.worldline.tech//images/post/owasp-appsec-europe-2017-feedback/owasp-appsec-europe-2017-feedback/google_csp.jpg does not exist }{: .align-center}
The study on which the presentation was based : CSP Is Dead, Long Live CSP!
AllStars
Those talks are part of a track called “AllStar”. Speakers are considered as the best of the best in hacking. I was impressed on how hackers can coutinuously find security bypasses whatever the protections.
”DOM based Angular sandbox escapes “, by Gareth Heyes
The first one showed us how Angular’s expression sandbox can be bypassable. Angular team tried to fix this by reenforcing controls in their parser but ethical hackers and security professionnals were always able to bypass those controls. They’ve continously provided lots of XSS vectors via complex scriptings (called gadgets) to bypass the sandbox. Result: Angular gave up and announced that they have removed the expression sandbox as for AngularJS 1.6 which means that they will do no more effort to block gadgets execution. I took inspiration from a part of this talk for my TechForum 2017 presentation.
{ https://blog.worldline.tech//images/post/owasp-appsec-europe-2017-feedback/owasp-appsec-europe-2017-feedback/angular_sandbox_escapes.jpg does not exist }{: .align-center width=“400px”}
”Exploiting the unexploitable with lesser known browser tricks “, by Filedescriptor - Slides
A young guy from Cure53 (German cybersecurity firm) - his identity is hidden behind the filedescriptor avatar - explained to us how he won some previous bug bounties (and how much money he earned for some of them - until 6000$!). A very skilled white hacker! The show/demo was interesting because it also teached us how hackers think. Very different than our way of thinking!
{ https://blog.worldline.tech//images/post/owasp-appsec-europe-2017-feedback/owasp-appsec-europe-2017-feedback/hack_in_action.jpg does not exist }{: .align-center width=“400px”}
DevSecOps
”How to put the Sec in DevOps “, by Helen Bravo - Slides Movie
Part of the DevSecOps track, this talk explained how to integrate security in DevOps and which kind of security tools can be used in each step of the process (Developement, CI, DI, ..).
When CI breaks (and it breaks) it impacts everyone and everything in the process. Creating a significant delay in the release cycle. In order to avoid build breaks you should start implementing security before the CI stage. If you have 365 developers and each developer breaks only a single build once a year (usually much more), you have an average of one build break per day.
{ https://blog.worldline.tech//images/post/owasp-appsec-europe-2017-feedback/owasp-appsec-europe-2017-feedback/DevSecOps_2.jpg does not exist }{: .align-center width=“600px”}
”Don’t Learn, Don’t See, Don’t Run: Application Security for DevSecOps “, by Joseph Feiman - Slides Movie
This talk described how security can be integrated to DevOps. Which kind of security tools or services suits for secure DevOps (SAST, DAST, RASP…)?
DevSecOps is not just culture. It is about technology, to a high degree. DevOps requires incremental, continuous, instantaneous and transparent Sec Sec should not distract Dev and Ops from doing DevOps DevOps will adopt Sec only if they don’t have to learn, see and run it
Other quotes :
We have entered into:
- New era of AppSec
- Next generation of technologies: self-testing, self-diagnostics, self-protection,DevSecOps-enabled SAST
- New markets, new demands: transparency, speed, incremental and continuous
- New paradigms: Cloud, DevSecOps, …
- New competitors: Previously ignored or not noticed – e.g. OSS,GoogZon
Some expectations :
Security as service will beat tools:
- By 2018, use of SAST-as-a-cloud-service will exceed use of SAST-as-a-tool, enhancing DevSecOps transparency and scalability.
- Through 2020, more than 25% of enterprises that adopted DevOps will also adopt DevSecOps-enabled SAST.
- Through 2020, use of DevSecOps-enabled SAST will exceed the use of traditional SAST.
- By 2019, open source will not offer SAST comparable with commercial SAST in accuracy, breadth and enterprise-class capabilities.
CISO (SDLC)
”Incremental Threat Modelling “, by Irene Michlin - Slides Movie
This talk explained how to implement an incremental threat modeling based on the STRIDE classification.
{ https://blog.worldline.tech//images/post/owasp-appsec-europe-2017-feedback/owasp-appsec-europe-2017-feedback/stride_modeling.jpg does not exist }{: .align-center width=“400px”}
Why create application threat models?
Threat modeling identifies risks and flaws affecting an application, no matter how old or new that application is. The threat modeling process offers a strategic practice by which you can think about a system’s characteristics. It also provides visibility into weaknesses that may affect not only the application, but potentially the entire organization.
When should threat modeling take place in the SDLC?
While threat modeling should take place as early as possible, it’s still a very useful activity no matter how close an application is to deployment or has been in production. While an app may have reached the end of its development cycle, you can still pick up threat modeling within the support cycle. Threat modeling offers perspective into potential flaws in the system. A thorough assessment informs your organization about the current design-level security stance of an application. Therefore, through threat modeling, you’re able to make an informed decision about investing further in that system.
Threat modeling - Synopsys
Hacker
”Boosting the security of your Angular application", by Philippe De Ryck - Movie
One of my favorite talks. Philippe De Ryck is one the most active speakers about Angular security hardening. This talk was very useful and up-to-date. New browser features and coming standards have been discussed (sameSite cookie attribute, cookie prefixes, sub-resource integrity, …). We’ve seen an overview of Angular security hardening (CSRF, XSS, JWT) but also some insights on Authorization header vs Cookies, JWT weaknesses, …
{ https://blog.worldline.tech//images/post/owasp-appsec-europe-2017-feedback/owasp-appsec-europe-2017-feedback/angular_hardening.jpg does not exist }{: .align-center}
"Don’t trust the DOM: Bypassing XSS mitigations via Script gadgets", by Sebastian Lekies, Krzystof Kotowicz and Eduardo Vela Nava - Slides Movie
A very interesting talk which synthetized a security research work done by google team members. The aim of this study was to compare JavaScript frameworks protections against XSS.
What struck me: almost all JavaScript frameworks are vulnerable against XSS by using gadgets (complex scriptings) whatever existing protection (WAFs, XSS filters, HTML sanitizers, CSP).{ https://blog.worldline.tech//images/post/owasp-appsec-europe-2017-feedback/owasp-appsec-europe-2017-feedback/js_framework_comparison.jpg does not exist }{: .align-center}
AngularJS 1.x is not well ranked mainly because of its expression sandbox (but Angular 2 has not been tested) - React and Ember are well ranked. Authors promotes the precompiled templates feature of Angular 2 (AOT).
A novice programmer, today, cannot write a complex but secure application.The task is getting harder, not easier. We need to make the platform secure-by-default(Safe DOM APIs, Better primitives in the browser, Build-time security). We need to develop better isolation primitives (Suborigins, < iframe sandbox>, Isolated scripts)
Lightning Talk
"AngularJS + CSP: A Perfect Match or Unhappy Marriage?", by David Johansson
How to use Content Security Policy headers with AngularJS? The good and the bad in configuring CSP in AngularJS.
This was a good introduction on how CSP and Angular framework interact together. Even if it was related to AngularJS, most of the recommendations are still valid for Angular 2+
We’ve seen CSP in details (directives, CSP versions 1, 2 and 3, whitelist/nonce/strict-dynamic strategies) and the ngCSP Angular directive which allows applying CSP for the framework itself (avoid eval() function call, …). The impact of CSP on Angular application’s performance was also part of this talk.
Conclusion
Security must be addressed in light of DevOps. Fully integrated, not separated. Implemented with methods and tools. Spread and shared by developers to become a reality.
This event was very security-oriented with a foot in the hacking world. Sometimes the border between security professionals and hackers is thin. White hats or ethical hackers often behave and think like malicious hackers in a controlled environment in order to provide efficient experience and feedbacks.

My only regret: I was a single attendee from Worldline and as my profil is more related to Developer and Hacker topics, I focused my attention on those tracks. I missed a lot of the other ones. I hope we will be more next year from Worldline for a better conference covering:)
But I learned a lot about JS framework security and especially Angular. Their weaknesses and strengths. How to mitigate and protect them against vulnerabilities and new threats. This was my priority for this event and I can say that, from that point of view, I’m definitely not disappointed!
Last thing: enjoy the slides and videos from the conference!